In this day and age, where data is the new oil, one of the most horrifying things that can go through one’s head is the fear of having one’s online account information stolen or of being unable to access the account at all. Even though this problem can be traced back to a number of different causes, the most important one is that there is insufficient security in place. This security deficiency can be broken down into two categories: negligence and poor security practices, both of which the vast majority of users either intentionally or unintentionally end up following.
Page Contents:
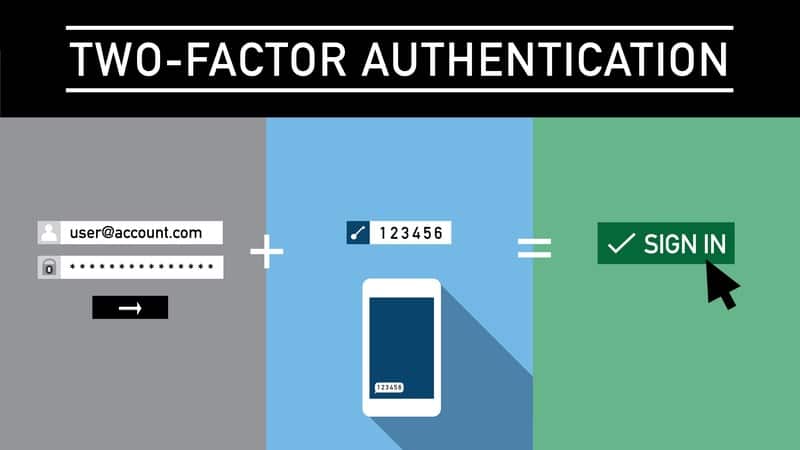
Increasing the level of protection on all of your online accounts by using two-factor authentication (also known as 2FA) is one solution to this predicament. In this manner, even if someone gains access to your password through hacking or disclosure, your account won’t be available until it is authenticated by the second factor (2FA verification token).
However, it appears that a significant number of users are either unaware of the availability of two-factor authentication or do not make use of it. Therefore, in an effort to make things more understandable, here is a tutorial on two-factor authentication that addresses some of the most often asked topics regarding 2FA.
What Is Two-Factor Authentication (2FA)?
Two-factor authentication, also known as 2FA, is a subset of multi-factor authentication (MFA), a method that adds an additional layer of security to your account by requiring you to authenticate your logins with more than one piece of information.
In a perfect world, when you log in to an online account using your username and password, the password will operate as the initial step in the authentication process. You won’t be able to access your account until the service ensures that the password you entered is correct and then grants you permission to do so.
If someone gets a hold of the password to your account, they will easily be able to log in and use your account. This strategy is one of the difficulties, as it is not the most secure option. To put it another way, this is precisely the point at which the presence of a second element becomes important.
During the process of logging into your account, a second factor provides an additional layer of authentication for your account. This second factor can be set up in a number of different ways. If it is turned on, after correctly entering the password for your account, you will be prompted to enter a verification code that will only be good for a set amount of time before it expires. This is done to ensure that the person accessing the account is who they claim to be. After passing the verification process, you will be given permission to access the account.
Two-factor authentication (2FA) is sometimes referred to as two-step verification (2SV), as with Google. This naming convention difference is dependent on the service that is implementing the process. Despite this, the core operating principle of both continues to be the same, despite the fact that they have different names.
How Does Two-Factor Authentication (2FA) Work?
In the preceding section, it was indicated that two-factor authentication requires the usage of a second factor (in addition to the first factor, which is the password) to complete an identity check while logging in. This second factor is known as the “second factor.”
Before an end-user is allowed to log in and begin using a service, apps, and websites that use two-factor authentication (also known as 2FA) demand that they verify at least two of the following elements (also known as pieces of evidence) as being true.
i. Knowledge – something that you know
ii. Possession – something that you have
iii. Inherence – something that you are
In most situations, the Knowledge factor can be something like your account password or a personal identification number (PIN), while the Possession factor can be something like a USB security key or authenticator fob, and the Inherence factor can be your biometrics such as your fingerprints, retina, or other similar features. This will give you a better idea of what constitutes each of these different factors.
In order to verify your identity on the service when you log in, you will be required to enter either of the two verification factors, between Possession and Inherence, in addition to the Knowledge factor. Once you have 2FA set up and running on any of your accounts, you will be required to enter either of the two verification factors, between Possession and Inherence.
After that, you are presented with two choices for the second authentication technique you want to use, which rely on both the resource you want to keep secure and the service you are utilizing. You have two options for verifying your identity: either you can use something called Possession, which may be any kind of physical security key, or you can use a code generator app on your smartphone, which will give you a token that can only be used once. You might also use Inherence, which is facial verification and other similar features, as a secondary security verification element for your account. Several providers now offer these features.
Is Two-Factor Authentication Foolproof? Are There Any Disadvantages to Using 2FA?
Now that you know what two-factor authentication is and how it operates, let’s take a deeper look at its implementation and the potential drawbacks of utilizing it on your account, if there are any.

To begin, it is important to note that despite the fact that the general consensus regarding the use of two-factor authentication among the vast majority of experts is generally positive and encourages people to enable 2FA on their accounts, there are unquestionably a few flaws with the implementation of the mechanism that prevents it from being a foolproof solution.
Most of these flaws, or rather vulnerabilities, result from poor implementation of two-factor authentication (2FA) by the services that use it, which can be problematic on a variety of different levels.
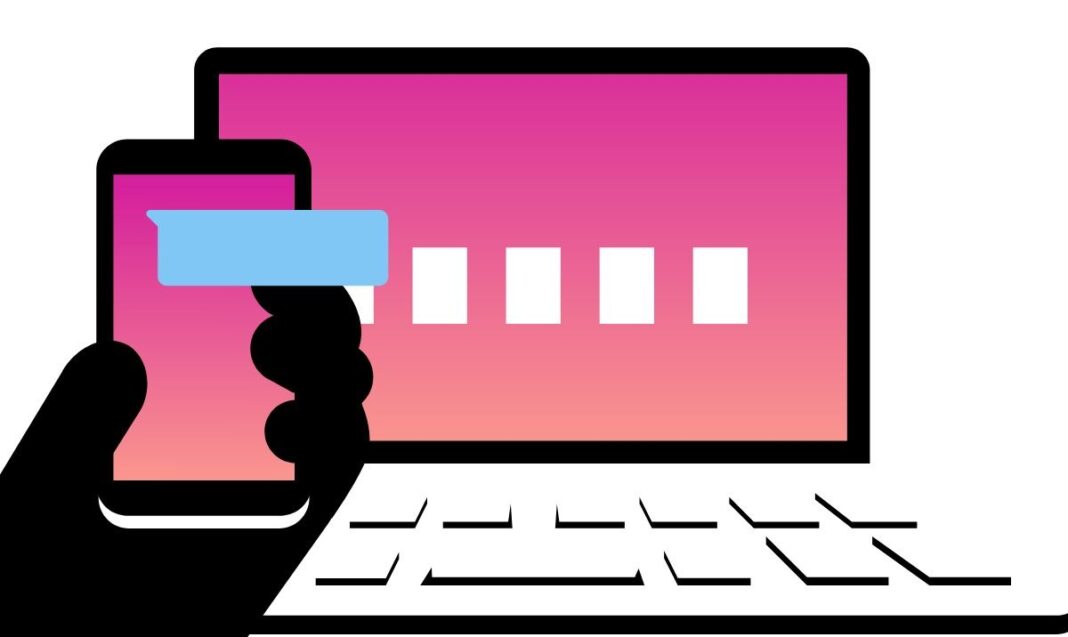
Consider the following situation, which will give you an idea of a bad (read: useless) implementation of two-factor authentication: you have two-factor authentication set on your account, and it uses your mobile number. In this configuration, the service will send you an OTP via SMS, and you will need to use that OTP in order to authenticate your identity. However, due to the fact that the second factor is being transmitted across the carrier in this scenario, it is vulnerable to a wide variety of assaults, and as a result, it is not secure in and of itself. As a direct consequence, the implementation in question may not be as successful at protecting your account as it should be.
In addition to the instance described above, there are a number of other scenarios in which two-factor authentication could be susceptible to a variety of other kinds of assaults. Some of these scenarios include instances in which a website or app that uses the mechanism has an incorrect implementation for token verification; does not have a rate limit, which makes it possible for someone to brute-force their way into the account; allows the same OTP to be sent multiple times; or relies on improper access control for backup codes, amongst other scenarios. All of these things can lead to vulnerabilities, which can make it possible for someone with the appropriate knowledge and skill set to circumvent the poorly constructed two-factor authentication scheme and gain access to the targeted account.
In a similar vein, another circumstance in which two-factor authentication might be troublesome is when you utilize it in a careless manner. For instance, if you have two-factor authentication enabled on an account using a code-generator app and decide to switch to a new device but forget to move the authenticator app to the new phone, you may be completely locked out of your account. This can be avoided by moving the authenticator app to the new device before you switch devices. And as a result, you run the risk of ending up in a scenario in which it will be difficult to regain access to accounts of this kind.
When you utilize SMS to receive your two-factor authentication token, this is yet another scenario in which using two-factor authentication might occasionally work against you. If you are traveling and move to an area with bad connectivity, you run the risk of not receiving the one-time-use token through SMS, which can temporarily leave your account inaccessible to you. In this instance, if you do not receive the token, your account will be locked out. Not to mention the fact that you switch carriers but still using the same cell number for the multiple accounts that require two-factor authentication.
However, with all of that being said, there is one crucial factor that is at play here, and that is the fact that the majority of us are just average internet users, and we don’t use our accounts for questionable use-cases, so it’s not very likely that a hacker will target our accounts as potential attack vectors because of this. One of the most obvious explanations for this is that the account of an average user is not bait-y enough and does not offer much to gain for someone to spend their time and energy carrying out an assault on it.
As a result, rather than experiencing some of the significant drawbacks of two-factor authentication, which were discussed previously, you will benefit from it to the most extent possible. In a nutshell, the benefits of two-factor authentication (also known as 2FA) much outweigh its drawbacks for the vast majority of users, provided that 2FA is used responsibly.
Why Should You Use Two-Factor Authentication (2FA)?
If we continue to join up for an expanding number of online services, we are, in some sense, increasing the likelihood that our accounts will be compromised. Unless, of course, security procedures are in place to protect the security of these accounts and keep dangers at bay. In that case, the phrase “unless” should be removed.
Over the past few years, data breaches of some of the most popular services (with huge user bases) have leaked tonnes of user credentials (email addresses and passwords) online. This has put the security of millions of users worldwide at risk, as it enables a hacker (or any person with the know-how) to use the leaked credentials to access these accounts.
The fact that these accounts do not have two-factor authentication in place makes the entire procedure simple and uncomplicated for a hacker, which is already a major cause for concern. However, the situation becomes much direr when these accounts do not have two-factor authentication in place. Therefore making it possible for an easy takeover.
A one-time password (OTP) or an app/fob-generated token can be used to verify your identity if you use two-factor authentication on your account. This provides an additional layer of protection that is difficult to circumvent because it relies on the possession factor (something that only you have access to) to validate your identity.
Accounts that require an additional step to get into are typically not the ones on the radar of attackers (especially in large-scale attacks) and are thus somewhat more secure than accounts that do not implement two-factor authentication (also known as 2FA). Having said that, there is no getting around the reality that utilizing two-factor authentication does involve an additional step during the sign-in process. Despite this, the safety and calmness of mind resulting from the exchange make the hassle completely worthwhile.
Having two-factor authentication (2FA) set on your account can be helpful in a wide variety of situations, including the one that was described above, which is only one of those situations. In spite of the fact that two-factor authentication (also known as 2FA) does increase the level of protection afforded to your account, it is not a failsafe system, and as such, it must be implemented correctly by the service in order for it to be useful. In addition, the user must also properly configure their account, which should be done with care (a backup of all the recovery codes should be created) in order for the service to function to your advantage.
How to Implement Two-Factor Authentication (2FA)?
To enable two-factor authentication on your account, you must first complete a series of steps, and these processes vary according to the type of account you wish to protect with two-factor authentication. Whether it’s one of the most popular social networking websites, like Twitter, Facebook, or Instagram; a messaging service, like WhatsApp; or even your email account, these services do give the option to enable two-factor authentication (2FA), which will strengthen the security of your account.

Even though using strong and unique passwords for all of your different accounts is a fundamental security measure, in our opinion, you shouldn’t ignore two-factor authentication but rather take advantage of it if a service provides the functionality. This is especially important for your Google account, which is linked to most of your other accounts, as a recovery option, because if your Google account is compromised, it could also compromise most of your other accounts.
When discussing the best approach to implementing two-factor authentication, one of the safest methods is to use a hardware key that generates codes at predetermined intervals. This is one of the most secure techniques. However, code-generating applications from the likes of Google, LastPass, and Authy should function just fine for the ordinary user. In addition, some password managers available these days provide users with both a vault and a token generator, which can make the process even simpler for certain people.

